MDaemon supports Sender Policy Framework (SPF) to help verify sending servers and protect against spoofing and phishing, which are two common types of email forgery in which the sender of the message attempts to make the message appear to be coming from someone else.
Many domains publish MX records in the Domain Name System (DNS) to identify the locations permitted to receive mail for them, but this doesn't identify the locations allowed to send mail for them. SPF is a means whereby domains can also publish sender records to identify those locations authorized to send messages. By performing an SPF lookup on incoming messages, MDaemon can attempt to determine whether or not the sending server is permitted to deliver mail for the purported sending domain, and consequently determine whether or not the sender's address may have been forged or "spoofed".
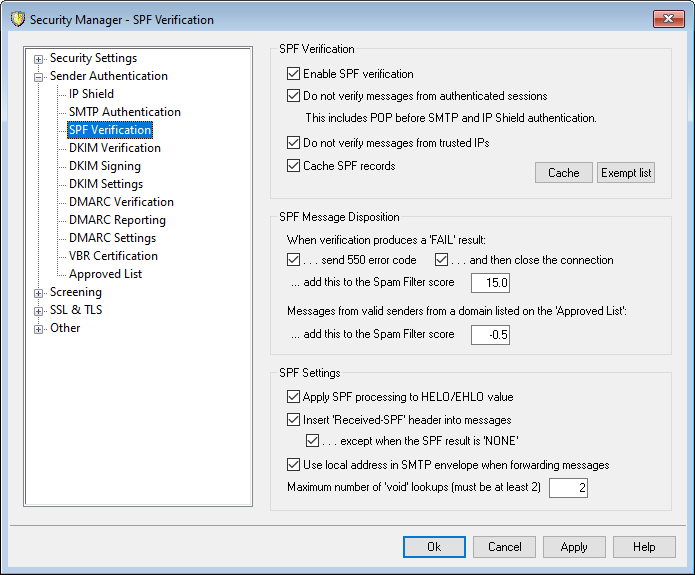
Use the options on this screen to configure your server's SPF settings.
For more information on SPF, visit:
SPF Verification
Enable SPF verification
When this option is enabled, MDaemon will perform a DNS query for SPF record data on each incoming message's purported sender, to ensure that the sending server is permitted to send messages on its behalf. The host MDaemon will verify is taken from the MAIL value passed during SMTP processing. SPF verification is enabled by default.
Do not verify messages from authenticated sessions
By default authenticated connections are exempt from SPF queries. Authenticated sessions include those verified via SMTP Authentication, POP before SMTP, or the IP Shield. Disable this option if you do not wish to exempt authenticated sessions from SPF.
Do not verify messages from trusted IPs
By default any message from a trusted IP address is exempt from SPF verification.
Cache verification results
By default MDaemon will temporarily cache each domain's SPF policy record obtained during the DNS query. Clear the checkbox if you do not wish to cache SPF policies.
Cache
This button opens the SPF cache, which lists all currently cached SPF records.
Exempt List
Click this button to open the SPF Exception List on which you can specify IP addresses and email addresses that you wish to be exempt from SPF lookups. Email addresses are compared against the SMTP envelope value (not the message's "From:" header). If you wish to exempt all of a domain's email addresses, then use the wildcard address "*@example.com" to do so for that domain. By using the prefix "spf" in front of a domain name (e.g. "spf example.com") MDaemon will append that domain's SPF record to every SPF lookup result. In this way you can have (for example) your MX provider treated as a valid SPF source for all senders.
SPF Message Disposition
When verification produces a FAIL result:
...send 550 error code
Click this check box if you want a 550 error code to be sent when the result of the SPF query is "Fail".
...and then close the connection
Enable this option if you want the connection to be closed immediately after sending the 550 error code.
...add this to the Spam Filter score
Specify the amount that you wish to add to the message's Spam Score when it fails to pass SPF verification.
Messages from valid sender from a domain listed on the 'Approved List'
...add this to the Spam Filter score
Specify the amount that you wish to add to a message's Spam Score when SPF confirms that it originated from a domain found on the Approved List.
|
Ordinarily the value specified here should be a negative number so that the spam score will be reduced for the approved messages. |
SPF Settings
Apply SPF processing to HELO/EHLO value
The option applies SPF verification to the value passed in the HELO or EHLO command at the beginning of the SMTP process. It is enabled by default.
Insert 'Received-SPF' header into messages
Click this option if you want a "Received-SPF" header to be inserted into each message.
...except when the SPF result is 'NONE'
Enable this option if you do not wish the "Received-SPF" header to be inserted into a message when the result of the SPF query is "none".
Use local address in SMTP envelope when forwarding messages
Enable this option if you want all mail forwarded by MDaemon to use a local address in the SMTP envelope. This helps reduce problems associated with forwarding. Normally, forwarded messages are sent using the email address of the original sender and not the email address that is actually doing the forwarding. In some situations, using a local address may be necessary in order to prevent the receiving server from falsely identifying the forwarded message as having a "spoofed" address. This option is enabled by default.
Maximum number of 'Void' lookups (must be at least 2)
This is the maximum number of void lookup results permitted in an SPF query before MDaemon generates a permanent error. A Void lookup is one that results in "domain does not exist" or "no answers exist." This value must be a least "2".
