Use this screen to configure MDaemon to verify DomainKeys Identified Mail (DKIM) signatures in incoming remote messages. When this feature is enabled and an incoming message has been cryptographically signed, MDaemon will retrieve the public key from the DNS record of the domain taken from the signature and then use that key to test the message’s DKIM signature to determine its validity.
If the signature passes the verification test, the message will continue on to the next step in the regular delivery process. Additionally, if the domain taken from the signature also appears on the Approved List, the message’s Spam Filter score will receive a beneficial adjustment.
For more on DKIM see: http://www.dkim.org/
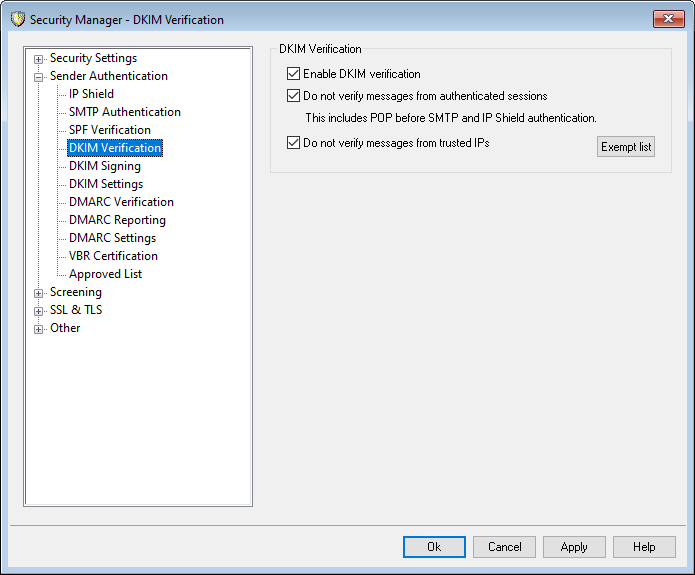
DKIM Verification
Enable DKIM verification
Click this option to enable DomainKeys Identified Mail verification of incoming remote messages.
Do not verify messages from authenticated sessions
Click this option if you want to exempt messages from cryptographic verification when the message session is authenticated. Authenticated sessions include those verified via SMTP Authentication, POP before SMTP, or the IP Shield.
Do not verify messages from trusted IPs
Use this option if you want connections from trusted IP addresses to be exempt from DKIM verification.
Exempt list
Click this button to open the exception list. Messages originating from any IP addresses specified on the list will not be subject to cryptographic verification.
Authentication-Results header
Whenever a message is authenticated using SMTP AUTH, SPF, DomainKeys Identified Mail, or DMARC, MDaemon will insert the Authentication-Results header into the message, listing the results of the authentication process. If MDaemon is configured to accept messages even when they fail authentication, then the Authentication-Results header will contain a code to identify the reason for the failure.
|
There is ongoing work via the Internet Engineering Task Force (IETF) on this header and the authentication protocols mentioned in this section. You can find more information on this at the IETF web site, located at: http://www.ietf.org/. |
DKIM Headers in Mailing List Messages
By default, MDaemon strips DKIM signatures from incoming list messages because those signatures can be broken by changes made to the message headers or content during list processing. If you would like MDaemon to leave signatures in list messages, you can configure it to do so by manually setting the following option in the MDaemon.ini file:
[DomainKeys]
StripSigsFromListMail=No (default is "Yes")
See:
